VoIP Encryption Protocols: SRTP, TLS, and ZRTP Guide
Voice traffic has become one of the most overlooked attack surfaces in enterprise security. As organizations migrate from legacy PSTN to IP-based voice, every call becomes a data stream subject to the same threats facing your applications, databases, and APIs.
Yet many enterprises still treat voice security as secondary to their broader IT security posture—a gap that sophisticated attackers actively exploit.
This guide covers VoIP encryption protocols, implementation challenges, and evaluation frameworks to help telecom leaders build voice infrastructure that's both secure and operationally sound.
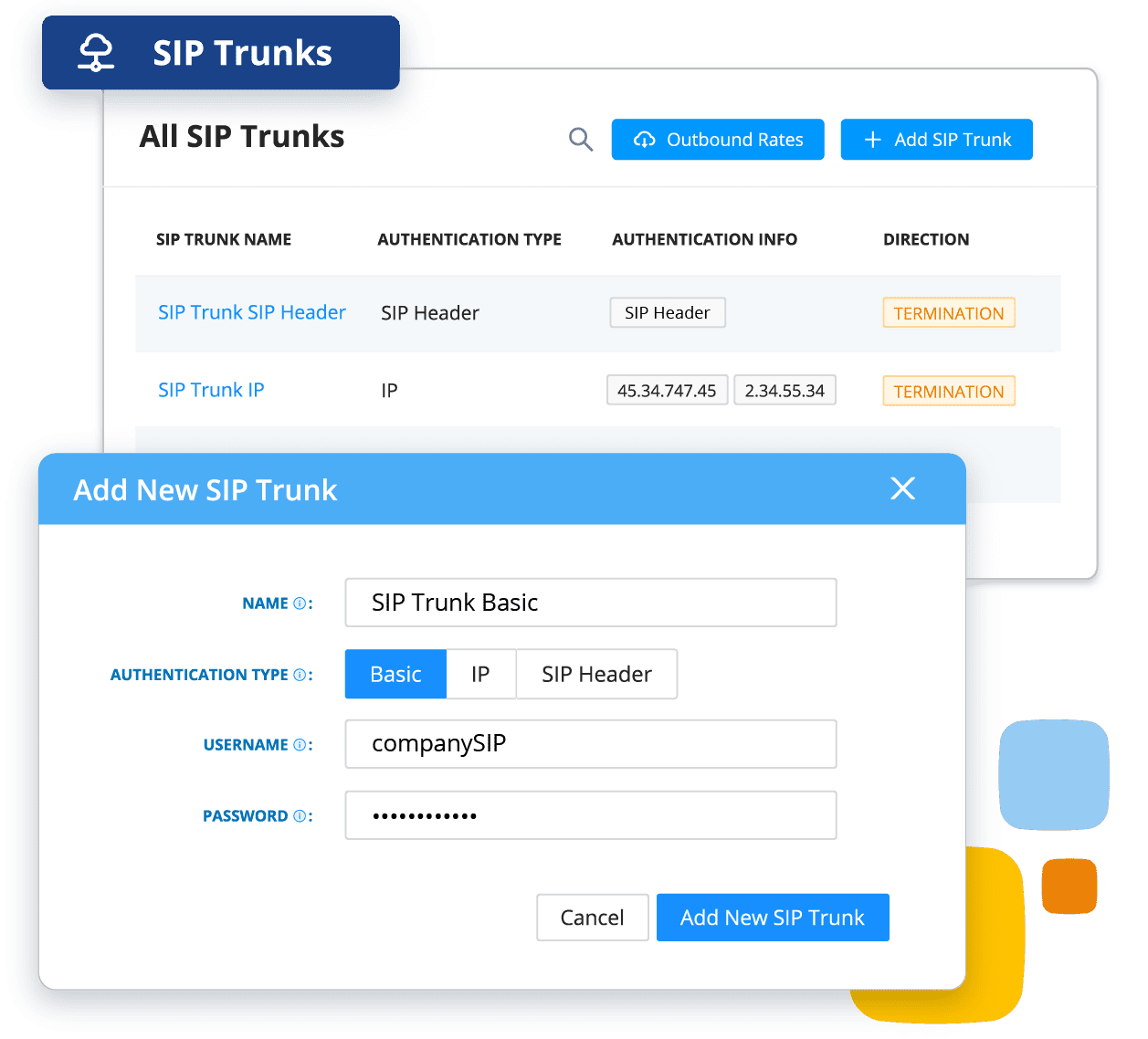
Need secure VoIP infrastructure for enterprise communications?
See how AVOXI helps businesses protect voice traffic with secure cloud communications, global coverage, and better visibility across their voice stack.
What VoIP Encryption Is and Why It Matters for Enterprise Communications
VoIP encryption secures voice data packets during transmission, converting readable voice traffic into protected streams that prevent unauthorized access, interception, or manipulation. Without it, your voice business communications travel as plaintext, exposing every conversation, caller identity, and routing detail to anyone positioned to capture the traffic.
Attacks can expand across multiple vectors, including:
- Eavesdropping on sensitive business conversations
- Toll fraud through hijacked SIP trunks
- Caller ID spoofing that enables social engineering
- Regulatory violations that carry real financial penalties
A single compromised trunk can expose thousands of phone calls and the customer data they contain.
Voice communications carry the same sensitive data and regulatory obligations as any other enterprise application and should be protected accordingly. The real challenge isn't whether to encrypt; it's how to deploy strong encryption across global voice infrastructure without sacrificing call quality or operational flexibility.
How VoIP Encryption Protocols Secure Voice Communications
Enterprise VoIP deployments rely on multiple encryption protocols working together to protect voice communications end to end. Unlike traditional telephony, where security was largely physical and controlled by carrier infrastructure, VoIP transmits voice as data packets across IP networks, creating attack surfaces that require protocol-level protection.
The two core protocols securing most enterprise VoIP traffic are:
- SRTP (Secure Real-time Transport Protocol), which encrypts the actual voice media
- TLS (Transport Layer Security), which secures the signaling traffic that sets up, manages, and tears down those calls
Together, they protect both what you say and the metadata about who you're calling, when, and for how long.
ZRTP (Zimmerman Real-Time Transport Protocol) represents a third approach, offering end-to-end encryption without centralized key management infrastructure.
SRTP (Secure Real-time Transport Protocol)
SRTP encrypts voice media streams in transit between endpoints. Even if your SIP signaling is protected with TLS, unencrypted RTP media streams remain vulnerable to packet capture. SRTP closes that gap by applying AES encryption to voice packets, ensuring intercepted traffic is unintelligible rather than audible, and it:
- Encrypts RTP media packets using AES-128 or AES-256 algorithms
- Provides packet authentication to detect tampering
- Adds minimal bandwidth overhead, typically under 10% compared to unencrypted RTP
- Integrates with key exchange mechanisms like SDES or DTLS-SRTP to establish encryption keys between endpoints
- Operates independently of signaling protocols for implementation flexibility
For enterprise deployments, SRTP implementation typically happens at the platform level rather than requiring endpoint-by-endpoint configuration. Platforms like AVOXI enable SRTP by default across their infrastructure, providing consistent media encryption without adding operational overhead.
One area worth examining during evaluation is how your platform handles key exchange, since that choice affects both security posture and interoperability with other systems.
TLS (Transport Layer Security) for SIP Signaling
While SRTP protects what you say, TLS protects how your call gets connected. SIP signaling contains sensitive metadata:
- Caller IDs
- Dialed phone numbers
- Call duration
- Routing information
- Authentication credentials
Without TLS, this traffic travels in plaintext, exposing call patterns and potentially enabling attackers to intercept credentials or manipulate routing.
TLS for SIP (often called SIPS) encrypts the signaling channel between endpoints and your SIP server or trunk provider using the same cryptographic framework that secures web traffic. For enterprise deployments, this:
- Keeps authentication credentials encrypted during transmission
- Protects call metadata from network-level surveillance
- Prevents man-in-the-middle attacks that could redirect calls or inject malicious commands
The practical challenge is ensuring consistent TLS implementation across your entire signaling path. A call may traverse multiple SIP proxies, session border controllers, and carrier interconnections, each requiring proper TLS configuration and certificate management.
ZRTP for End-to-End Encryption
ZRTP, developed by Phil Zimmermann (creator of PGP), establishes encryption keys directly between endpoints using a Diffie-Hellman key exchange—without relying on centralized key management infrastructure.
This peer-to-peer approach means ZRTP can protect media streams even when intermediate servers might be compromised, making it relevant for scenarios requiring absolute confidentiality, like:
- Executive communications
- Legal discussions
- Sensitive negotiations
That said, ZRTP's strengths come with real limitations. Both endpoints must support ZRTP natively, creating interoperability challenges with external parties or legacy phone systems.
The optional manual verification step adds friction most enterprise users won't consistently perform. And the peer-to-peer architecture complicates compliance monitoring and call recording, since the platform provider can't access the decrypted media stream.
For most enterprise voice infrastructure, SRTP with centralized key management provides the right balance of security, manageability, and operational simplicity. But ZRTP is worth considering in high-security environments where the additional protection justifies the complexity.
VoIP Encryption Implementation Challenges and Solutions
Deploying VoIP encryption across global enterprise infrastructure introduces operational complexity that often catches telecom teams off guard. The security case is clear, yet the implementation realities are where projects run into trouble.
Bandwidth and Latency Considerations
Encryption adds computational overhead at both endpoints, and the additional packet headers required by protocols like SRTP increase bandwidth consumption by approximately 10%–20% compared to unencrypted voice streams.
Legacy on-premises systems running encryption on underpowered hardware often struggle under load. This insufficient bandwidth creates packet loss and jitter that encryption can't fix, and it may worsen if Quality of Service (QoS) policies aren't configured to prioritize encrypted voice traffic.
Latency is the more critical concern: voice quality degrades noticeably once total end-to-end latency exceeds 150 milliseconds, and when routing encrypted calls across continents through multiple network segments and session border controllers, those milliseconds accumulate.
The solution: Migrating to cloud-based platforms with optimized encryption implementations and distributed points of presence can minimize latency penalties. You should also conduct baseline performance testing before full deployment, measuring latency and packet loss across your actual call paths, and verify that QoS policies correctly identify encrypted voice packets.
Key Management and Distribution
Managing encryption keys across a distributed VoIP system is one of the most operationally demanding aspects of any deployment. A single misconfigured key exchange can result in failed call establishment, one-way audio, or complete service disruption—issues that become exponentially harder to diagnose when they occur intermittently across global networks.
The solution: For effective key management for enterprise VoIP, use:
- Automated key exchange protocols that handle session key generation without manual intervention
- Centralized systems that provide visibility into key lifecycle status
- Certificate-based authentication for SIP endpoints
- Regular key rotation policies (typically every 30–90 days depending on your risk profile)
- Secure key storage, often leveraging hardware security modules (HSMs) in sensitive environments
Your key management approach should also account for disaster recovery. What happens when a primary key server becomes unavailable? How quickly can you revoke compromised keys across your global infrastructure? These require documented procedures and tested failover mechanisms.
Best Practices for Securing VoIP Networks Beyond Encryption
Encryption protects data in transit, but comprehensive voice security requires a layered approach that addresses vulnerabilities across your entire infrastructure. Even with strong protocols in place, your network remains exposed if access controls are weak or suspicious activity goes undetected, so be sure to implement best practices:
- Network segmentation and VLANs. Create an essential security boundary by isolating voice traffic from general data traffic. This reduces the attack surface, limits lateral movement if other network segments are compromised, and makes it easier to apply security policies tailored to voice traffic patterns.
- Identity and access management. Prevent unauthorized users from reaching your voice infrastructure. Multi-factor authentication for administrative access, role-based permissions, and regular access log audits catch the credential-based attacks that account for a significant share of data breaches.
- Real-time monitoring and analytics. Provide visibility that encryption alone can't deliver. Platforms like AVOXI can detect anomalies, such as unusual call patterns, unexpected geographic origins, or sudden spikes in failed authentication attempts, before they escalate into incidents.
- Session border controllers (SBCs). Use these as gatekeepers at the network edge, inspecting and controlling VoIP traffic before it reaches internal infrastructure. They protect against denial-of-service attacks, block suspicious call patterns associated with toll fraud, and enforce security policies consistently across all voice sessions.
A defense-in-depth strategy recognizes that no single control is sufficient. Combining encryption with network segmentation, access controls, and continuous monitoring creates multiple barriers that meaningfully reduce risk exposure while maintaining the call quality your business depends on.
Evaluating VoIP Encryption Solutions for Your Organization
Selecting the right VoIP encryption solution requires a structured evaluation process that balances security requirements with operational realities. Treating encryption as a checkbox feature leads to implementations that look good on paper but create security risks in practice.
When reviewing any solution, keep these essentials in mind.
Security Requirements Assessment
Before evaluating vendors or protocols, map your compliance landscape, including these frameworks:
- PCI DSS mandates encryption for cardholder data transmission, which extends to voice channels used for payment processing.
- HIPAA requires appropriate safeguards for protected health information, including voice conversations between providers and patients
- Financial scrutiny under GDPR, SOX, and industry-specific frameworks can also apply.
Document which regulations apply to your voice traffic and whether requirements cover real-time transmission, stored recordings, or both.
Follow that with a threat modeling exercise specific to your voice infrastructure, and consider:
- Eavesdropping risks for sensitive customer conversations
- Toll fraud exposure through credential theft
- Compliance penalties from unencrypted voice traffic
- Reputational damage from security incidents
If your infrastructure spans multiple countries, factor in data sovereignty requirements and encryption standards that vary across jurisdictions.
Cost-Benefit Analysis Framework
VoIP encryption carries real costs, such as:
- Encryption-capable infrastructure
- Security feature licensing
- Implementation labor
- Ongoing key management overhead
- Potential latency impacts
- Additional bandwidth consumption
- Complexity of managing encrypted voice across multiple regions or carriers
However, the benefits can offset these costs. Quantify risk reduction in terms your finance team can evaluate. For regulated industries, compliance violations can reach seven figures. Even outside regulated sectors, the reputational damage from exposed customer conversations can be severe. Encrypted VoIP infrastructure often delivers operational benefits beyond security, including:
- Better analytics
- Centralized management
- Simplified vendor relationships
Platforms integrating VoIP encryption with broader voice management can lower total cost of ownership compared to fragmented legacy systems. Implementing encryption as part of a broader voice modernization initiative typically delivers better ROI than treating it as a standalone security project.
Implementation Planning and Testing
A successful deployment starts with a phased implementation plan beginning in a controlled environment. Select a representative subset of your voice infrastructure that includes the device types, network segments, and call patterns you'll encounter at scale. Run the pilot long enough to capture edge cases and performance variations across different traffic loads.
Your testing protocol should verify:
- Call quality metrics (MOS scores, jitter, packet loss, and latency with encryption enabled versus your unencrypted baseline)
- Interoperability across all device types and carrier connections
- Failover behavior during network transitions and disaster recovery scenarios
- Key exchange timing during call setup
- Whether your analytics platform can track encryption status in real time and alert on protocol failures
Before moving to full deployment, establish clear rollback procedures. Your team should be able to disable encryption for specific users, regions, or call paths without disrupting overall voice service.
To ease management and overall processes, you need to recognize voice as mission-critical infrastructure that requires the same security standards as your CRM, ERP, or financial systems.
Book a demo with AVOXI to see how it can benefit your business.