VoIP Fraud: Detection, Prevention, and Response Guide
Voice over Internet Protocol (VoIP) fraud can wipe out a telecom budget before anyone on your team spots a problem. Attackers abuse Session Initiation Protocol (SIP) trunks, Private Branch Exchanges (PBXs), and UCaaS connections to generate high-cost traffic, and organizations often find out after the invoice lands and the totals are already past dispute.
The scale of this issue is hard to ignore. Communications Fraud Control Association (CFCA) data, summarized in a telecom fraud losses report, puts 2025 global telecom fraud at $41.82 billion, with IRSF, toll fraud, and Wangiri all in the mix.
Meanwhile, the Public Interest Network estimates that US consumers alone lost $25.4 billion to phone scams in a recent 12‑month period, and the FTC Do Not Call report logged more than 2.6 million complaints in the 2025 fiscal year.
If you own enterprise voice, VoIP fraud is not an edge case—it's a board-level risk. This guide focuses on how you detect, prevent, and respond to fraud across global voice estates, using both processes and platforms like AVOXI to close the gaps between carriers, regions, and technologies.
Ready to secure your VoIP system from attackers and fraud?
AVOXI can help with careful, constant security maintenance to lower risk and stay on top of potential risks.
What Is VoIP Fraud, and Why Is It a High-Severity Risk for Enterprise Voice?
VoIP fraud is the unauthorized use of IP-based voice systems, such as SIP trunks, PBXs, UCaaS, and contact centers, to generate revenue for an attacker. They essentially turn your voice infrastructure into their billing engine, usually by driving traffic to international or premium-rate destinations they control or profit from.
Enterprise environments are prime targets because of scale and complexity, as they’re most likely dealing with:
- Separate PBXs in multiple regions and different local carriers, with additional UCaaS or CCaaS platforms on top
- Multiple dial plans, access models, and security postures for each system
- Five to ten voice providers, which translate to five to ten portals, CDR formats, alerting approaches, and contract terms
That fragmentation makes it harder to see fraud patterns early. A single compromised extension can send traffic out through multiple carriers, with no one system seeing the full picture until the invoices roll in.
Yet, the risk goes beyond direct call charges. Fraud incidents can:
- Consume engineering time
- Damage carrier relationships
- Force emergency routing changes that impact customer experience
Treating VoIP fraud as a core part of your voice architecture strategy, rather than a billing problem, puts you in a much better position to control it.
What Are the Most Common Types of VoIP Fraud?
Fraudsters use many tactics, but three types account for most of the financial damage in enterprise environments:
Toll Fraud and PBX Hacking
Toll fraud happens when an attacker gains access to your PBX, SBC, or SIP trunk credentials and uses them to make large volumes of outbound calls to high-cost international or premium-rate destinations—where the attacker benefits from inflated termination charges.
Common entry points include:
- Default or weak passwords on extensions
- Internet-exposed SIP ports without proper ACLs
- Unpatched PBX software
Once inside, attackers often set up call forwarding rules, auto-dialers, or new routes that bypass your normal policies. They take advantage of the natural benefits, size, and operations of enterprise phone systems:
- Speed: Automated tools can place hundreds of concurrent calls within minutes.
- Scale: A single trunk or extension can generate tens of thousands in charges.
- Blind spots: Distributed PBXs and multiple carriers make anomalous usage harder to see in real time.
Because the fraudulent calls originate from your authorized infrastructure, carriers treat them as legitimate traffic—leaving you to dispute or absorb the cost.
International Revenue Share Fraud (IRSF) and Premium-Rate Abuse
In international revenue share fraud (IRSF), attackers send calls from your VoIP network to numbers associated with revenue-share agreements—usually in remote or niche destinations with unusually high termination fees.
The attacker controls or has commercial arrangements with the destination range, so every minute of call time generates income for them. Premium-rate abuse follows the same pattern but focuses on services like international equivalents of 1-900 lines.
IRSF is difficult to spot without good baselines, as these look like valid calls to valid phone numbers. Without geographic restrictions, rate limits, or anomaly detection, you may only discover the pattern once the carrier bill highlights an unexpected spike to obscure destinations.
Wangiri (One-Ring) Fraud and Callback Scams
Wangiri fraud targets your users rather than your infrastructure. Attackers blast thousands of short calls—ringing once, then disconnecting—to numbers in your organization, relying on people calling back out of curiosity. Those callbacks terminate on premium-rate international numbers tied to the fraudster's revenue stream.
Callback scams extend this approach using social engineering: attackers leave voicemails claiming missed deliveries or banking alerts, prompting users to return the call and stay on the line while charges accumulate.
From your perspective, these are legitimate outbound calls made by real users, making Wangiri particularly dependent on traffic analytics and user education. Watch for patterns like many short calls to the same foreign number or sudden bursts of outbound traffic to countries where you don't normally do business.
How Do You Detect VoIP Fraud Early Using CDRs, SIP Signaling, and Behavioral Baselines?
Catching VoIP fraud early is mainly a visibility problem. You need a timely, consolidated view of usage across all carriers, regions, and platforms, plus clear expectations of what "normal" traffic looks like.
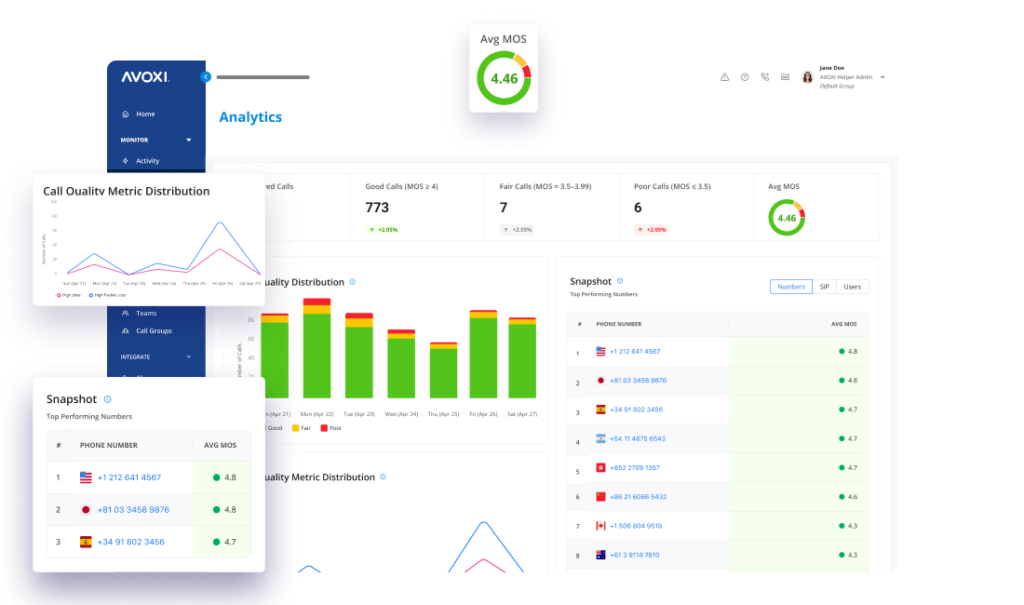
If every VoIP service provider offers a different portal and reporting cadence, your team ends up doing manual CDR pulls and spreadsheet analysis, which are often far too slow for attacks that unfold over hours. Platforms like AVOXI address this by aggregating traffic into one analytics layer with rule-based and behavioral monitoring built in.
What to Monitor Across CDRs, SIP Logs, and Traffic Patterns
For solid fraud detection, you and your teams need to know what to watch for.
In CDRs, priority indicators include:
- Sudden growth in outbound calls to specific country codes or premium-rate prefixes
- High volumes of calls during nights, weekends, or holidays relative to normal patterns
- Unusual clusters of very short calls, suggesting automated probing or callback scams
- Extremely long international calls that don't match typical business usage
In SIP signaling logs, watch for:
- Repeated registration or authentication failures from unknown IP addresses
- INVITE requests from geographies where you have no staff or infrastructure
- New or unexpected user agents compared with your approved devices and VoIP phones
- Rapid re-registrations using the same credentials from multiple endpoints
In real-time traffic views, monitor:
- Spikes in concurrent calls beyond forecasted peaks
- Concentration of traffic on a single trunk, region, or route that doesn't fit normal load-balancing behavior
- Shifts in domestic vs. international mix that don't align with known events or campaigns
Note: AVOXI surfaces these indicators through its Call Insights and traffic analysis tools, reducing the need to reconcile data manually across carrier portals and helping you move from retrospective billing reviews to near real-time monitoring.
How to Build Baselines and Alert on Anomalies without False Positives
To ease your day-to-day security maintenance, it’s essential to set up baselines for smarter tracking and alerts for greater visibility. Start with these four steps to establish a base plan:
- Analyze at least 30 days of traffic for each major segment: business unit, region, and use case.
- Capture metrics such as average and peak calls per hour, normal destination mix by country and trunk, typical call duration ranges, and expected after-hours traffic bands by site.
- Configure alerts based on relative changes rather than static numbers—for example, "international minutes exceed 200% of the 7‑day rolling average."
- Combine multiple conditions, such as destination + time of day + volume, for higher-confidence alerts and fewer false alarms.
On AVOXI, anomaly detection runs continuously across aggregated traffic, and a 24/7 monitoring team can review events before escalating them, helping you stay sensitive to true fraud attempts without overwhelming on-call engineers with noise.
How Do You Prevent and Mitigate VoIP Fraud Across SIP Trunks, PBXs, Carriers, and UCaaS?
Prevention is about building multiple layers of control so a single failure—like an exposed port, a compromised password, or a misconfigured dial plan—doesn't translate directly into large financial losses.
Because your voice environment likely spans on-premises PBXs, cloud platforms, and several carriers, consistency is just as important as strength.
Harden Your Voice Perimeter and Access Controls
Safeguard your perimeter and access controls with these critical measures:
- Deploy session border controllers between internal systems and external carriers to enforce signaling rules, authentication, and topology hiding.
- Restrict SIP access by IP, limiting registration and call setup to trusted networks and remote access paths such as VPN.
- Replace default passwords on all endpoints, enforce strong credential policies, and periodically rotate SIP and admin credentials.
- Keep PBX, SBC, and softphone software patched so publicly known vulnerabilities can't be exploited.
Use TLS for SIP signaling and SRTP for media so attackers can't intercept credentials or manipulate call setup.
To make this easy and safe, AVOXI provides encrypted SIP connectivity and carrier-grade security controls as part of its cloud voice fabric, helping you maintain a consistent perimeter even when underlying carriers differ by region.
Enforce Policy-Based Controls for Dial Plans, Routing, and Spend Limits
Update your policy for stronger VoIP security, following these steps:
- Design dial plans using least-privilege principles—only enable international and premium-rate routes for teams that genuinely require them.
- Apply geographic blocking for countries commonly associated with IRSF if you have no commercial reason to call them.
- Implement time-based rules that treat international traffic outside business hours as higher risk.
- Set per-account and per-trunk spend thresholds so, once exceeded, outbound calling is paused or restricted until reviewed.
By consolidating outbound routing and number management in AVOXI, you can define dial plan and spend policies centrally and apply them consistently across global operations, cutting down the chance that a forgotten trunk or regional carrier becomes the weak link.
Add Real-Time Detection and Automated Blocking to Stop Active Attacks
Detection without automatic containment still leaves you racing the clock during an incident, so be sure to implement these practices:
- Configure automatic blocking for specific country codes, prefixes, or individual numbers when traffic exceeds defined thresholds.
- Enable rate limiting or velocity controls that cap calls per minute or per hour from a trunk, extension, or IP address.
- Use dynamic deny lists so IPs responsible for repeated failed authentication are temporarily or permanently blocked.
- Combine alerts with scripted responses, such as disabling an extension and notifying an on-call engineer if multiple fraud indicators appear together.
AVOXI supports real-time traffic analysis, configurable blocking rules, and 24/7 monitoring, so suspicious activity can be contained quickly—often before it shows up as a noticeable cost line. That automation is especially valuable for nights, weekends, and holidays, when your internal team may not be watching dashboards in real time.
VoIP Fraud Incident Response: How Do You Contain Losses, Recover Service, and Prevent Recurrence?
Even with strong controls, you should assume that some fraud attempts will get through. Your incident response plan determines how much damage those attempts cause and should follow this wireframe:
- Contain the exposure. As soon as you confirm suspicious patterns, disable any clearly compromised accounts, trunks, or routes. Block traffic to the affected destinations, tighten temporary spend limits, and, if necessary, move high-risk workloads to alternative trunks with stricter controls.
- Restore safe service. Reset credentials on impacted systems, review firewall and SBC rules, and validate dial plans line by line to confirm attackers haven't left backdoors like hidden call forwarding or new outbound routes. For heavily targeted regions, bring traffic back online in stages while monitoring closely for recurrence.
- Run a post-incident review. Identify which controls worked, which failed, and where earlier detection could have reduced losses. Use that insight to adjust baselines, add new alerts, or tighten dial plans. If fragmented carriers made it hard to coordinate the response, that's often a catalyst to move more of your voice footprint onto a consolidated platform.
Many enterprises adopt AVOXI as part of that modernization effort. Because voice, analytics, number management, and fraud monitoring live in one place, you gain a consistent incident response playbook across countries and carriers instead of custom procedures for each vendor.
Talk with our team to review your current fraud posture and see what a more unified model could look like.